A new report has just found out that sensitive messages and other private data of users in the popular dating app, JCrush, have been breached. The database is no longer accessible and the leaks seemed to have been stopped but the fact remains that for a time the data leaks have exposed sensitive private data.
VPN review website known as vpnMentor says they discovered the data leak of the dating app. The report said that the data breach has exposed up to 200,000 users’ private information, preferences, and even private explicit conversations from members of the dating app. JCrush was acquired in 2018 by Northsight Capital, Inc. It is part of-of the Crush Mobile family of dating apps.
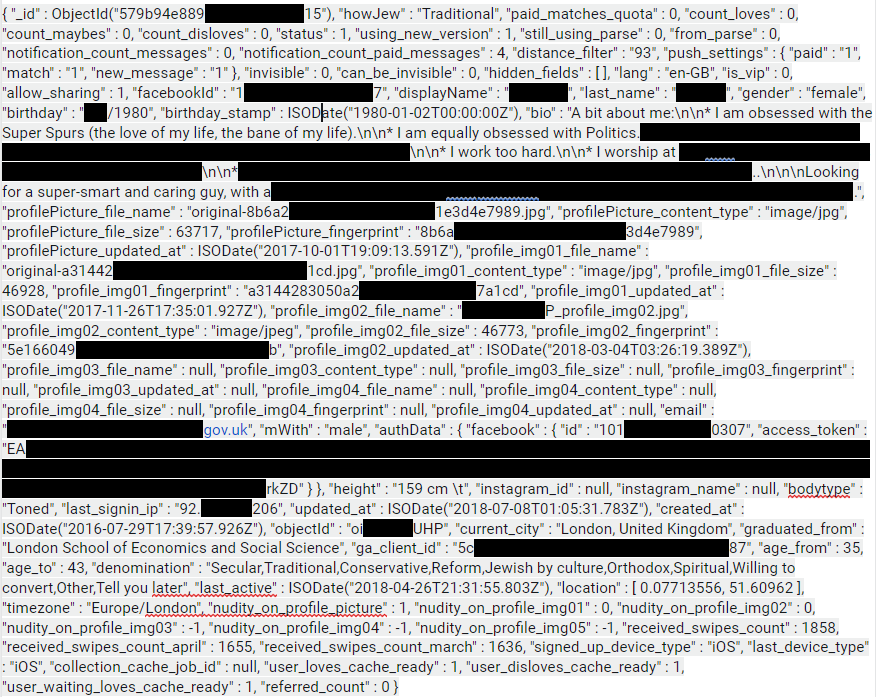
vpnMentor said that the data leak was so severe because of the nature of data that were leaked. Aside from the unencrypted private correspondences between users, personally identifying information were also exposed. These include first and last names of users, email addresses, Facebook tokens, full user profiles, and profile pictures. In addition, the data leak also includes information specific to the user’s usage of the dating app such as how many “swipes” a user received per month and when and where the user logged in from.
The data leak happened despite the fact that JCrush has been offering a special “incognito mode” to its users. While members thought that opting to enlist in this mode renders their privacy secured and safe, it seems that it was not the case as the leak can still potentially expose those members who wish to remain anonymous in their dating activities. This is true especially for dating app members who are engaged in unsolicited activities and members who are hiding sensitive information including their marital status.
The data leak was discovered through a huge web mapping project conducted by vpnMentor using a port scanner that examines known IP blocks. This is then evaluated for vulnerabilities, such as potential data exposure and breaches.
To prevent future data leaks, vpnMentor suggest that companies should secure their servers, implement proper access rules, and never leave a system open to the internet especially if the system requires authentication.
Free Tutorial: Our step-by-step guide to starting your own website for fun or profit
If you're tired of censorship and dystopian threats against civil liberties, subscribe to Reclaim The Net.