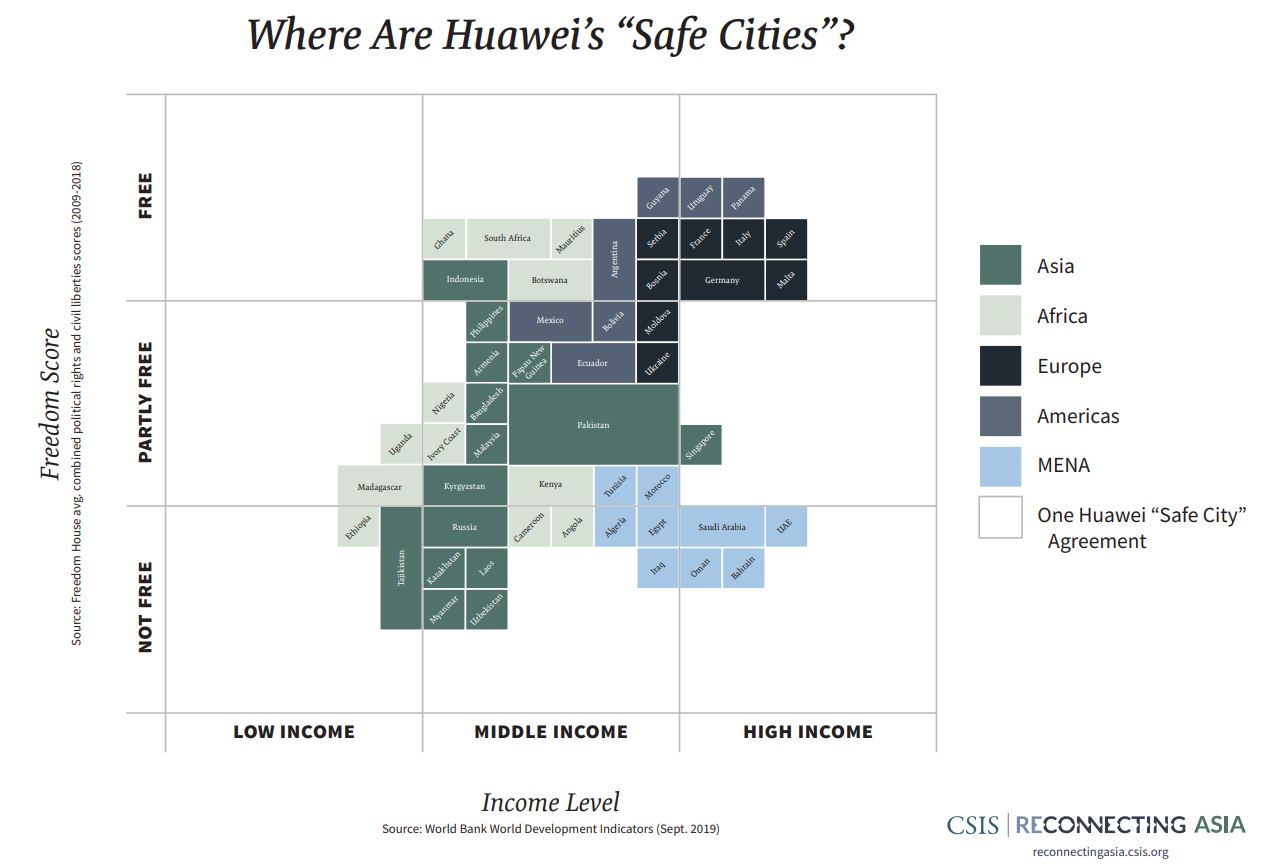
Huawei has just leveled up its spying efforts. Why spy on people directly, when they can provide a service that lets authoritarian governments spy on people? Either way, Huawei is getting the data, but the latter is easier to sell to oppressive regimes.
The Ugandan government is one such client. After the Assistant Inspector General of Police was murdered in 2017, they decided to set up CCTV surveillance across the African nation, making them the fourth in Africa to purchase security equipment from Huawei – after Kenya, Egypt and Zambia.
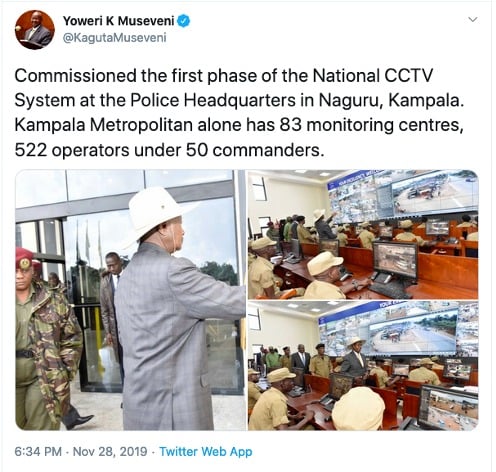
This movement began in July 2019. The first phase covered the Kampala metropolitan area and was completed late last year. The second phase began early this year and aims to cover the rest of the country in CCTV cameras for constant surveillance.
Huawei’s predictably named “Safe City” program includes 12 African nations in total. Conveniently, at the time of writing, all mentions and links to any such information have been completely scrubbed from Huawei’s website’s at the time of this writing.
“Huawei’s Safe City initiative undoubtedly threatens human rights in Uganda, including the right to peaceful assembly and association as the country prepares for [the] 2021 general elections,” said Dorothy Mukasa, CEO of Unwanted Witness, a Ugandan human rights organization.
As if all that wasn’t bad enough, we’re not just talking about regular old CCTV cameras watching every inch of the country. We’re talking about facial recognition technology and hundreds of “monitoring centers” in each city whose sole job is to watch every single camera feed constantly.
This surveillance system will be directly tied not just to law enforcement, but also to the revenue service and immigration office.
This isn’t the first time Huawei has been involved in this sort of “proxy mass surveillance”. Back in 2009, they were heavily involved in the CarrierIQ scandal that had governments and service providers spying on all of their users. CarrierIQ was unremovable spyware pre-loaded onto all Android, iPhone, and Blackberry devices. It reported back all manner of data, including passwords and credit card information, all sent over an unencrypted network in plain text.
If you're tired of censorship and dystopian threats against civil liberties, subscribe to Reclaim The Net.