
Telegram Founder Reveals US Government’s Alleged Covert Maneuvers to Backdoor The App
US authorities allegedly sought backdoors into Telegram’s encryption.

US authorities allegedly sought backdoors into Telegram’s encryption.
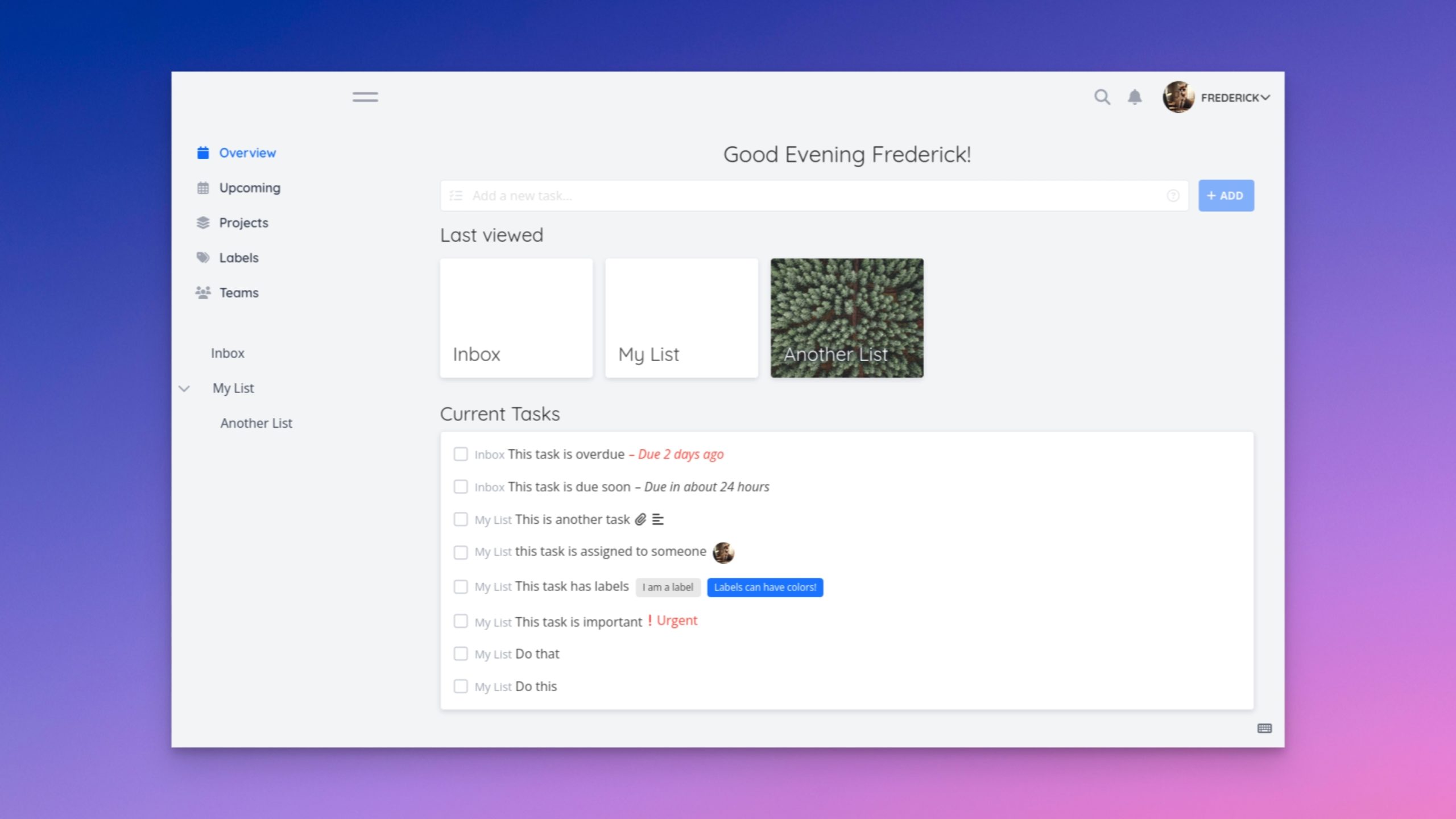
Reclaim ownership of your to-do list.

Make these changes to enjoy more online freedom and privacy.
Never leave your router in its default state.


But 2-factor authentication was only mandated after the breach.

Protect your notifications from Big Tech and government snooping.
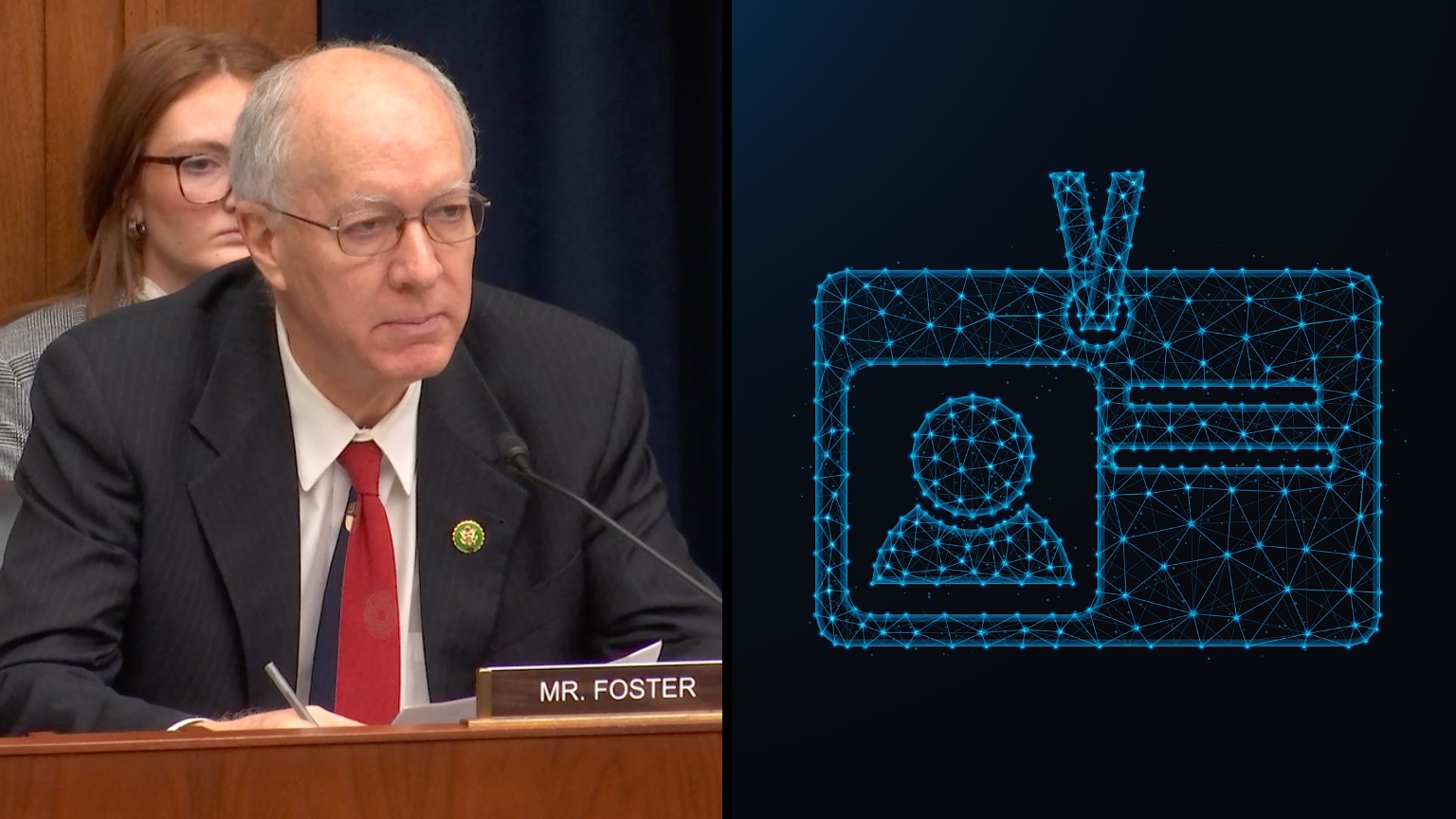
Several Democrats praised digital ID and CBDCs during a recent hearing.

The attack took place just after Rumble became home to January 6th CCTV footage, the CEO notes.