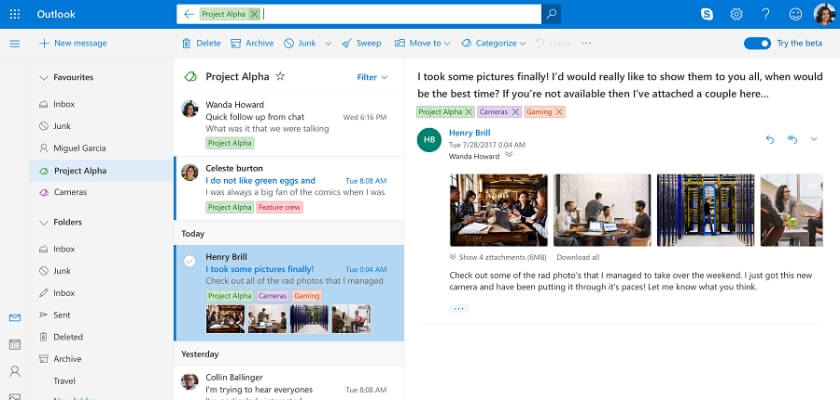
This year, in January, Microsoft already faced a big data breach where hundreds of millions of email passwords were hacked.
But now it looks like their Outlook servers have also been compromised.
Microsoft has revealed to TechCrunch that a hacker was able to a “limited number” of access Outlook.com accounts for several months by using the credentials of agents working in customer support. It is speculated that the credentials were used in a 3-month span, ranging from January 1st to March 28th, 2019.
It was revealed that hackers could see usernames, email addresses, subject lines, and folder names, but it is said that they couldn’t access the email content itself, attached files or passwords. While passwords might not be in danger, Microsoft still addressed this issue and sent an announcement that the users should change their passwords and be careful about any email scams like phishing, emails that ask for any sort of payment or other similar suspicious looking mail.
The credentials used for the hack have been disabled, and some details about the breach are still unclear – for example how many accounts were affected and how many email addresses have been gathered, but judging the last breach, this number could go up to millions, even though Microsoft has said that the number would probably be lower.
It’s also still not clear how the hacker was able to get the credentials needed for such action.
The breach represents a scary violation of privacy – the data could be used not only for phishing and similar scams, but the subject lines and other information could be used to piece the puzzle together about the users and to use that information for identity theft or other criminal activities.
As the hackers used the customer support agent’s accounts for the hack, they could look into any emails and even the two-factor security authentication was not able to prevent them from gathering info.
Microsoft is currently sending out emails notifying users about the hack and what they could do to protect themselves, how they should change their password even if they might not be initially targeted by the hack.
Hackers could also see the other email addresses you were communicating with, so the whole list of gathered addresses and usernames could be longer than just the hacked ones.
In a statement to TechCrunch Microsoft said:
“We addressed this scheme, which affected a limited subset of consumer accounts, by disabling the compromised credentials and blocking the perpetrators’ access…Microsoft regrets any inconvenience caused by this issue, and you should stay assured that Microsoft takes data protection very seriously and has engaged its internal security and privacy teams in the investigation and resolution of the issue, as well as the additional hardening of systems and processes to prevent such recurrence.”
Some of the Microsoft engineers also said that the confusion about what the hacker actually has arisen from asking some sensitive questions – like whose accounts the hacker accessed, which customer support agent’s credentials were used and so on, as the term “support agent” could be referring to both the tech support as well as the other staff, engineers who are working with Microsoft’s enterprise clients. Agents working for enterprise clients often have more access to details as they handle more complex issues and assignments.
Currently, the general opinion of the media and some experts is that there is only a small, limited number of users’ data that is compromised, but without further details, we can only hope that this is the case.
Microsoft revealed that in the events following this breach, they increased detection and monitoring for the affected accounts, just to be sure there’s no unauthorized access for those accounts or any suspicious or ill behavior.
I hope that Microsoft gives more information to the public soon so the users know what is happening with their data and what who was responsible for the hack, and what intention did they have while they were doing it.
Here is the full letter Microsoft sent to affected customers:
Dear Customer
Microsoft is committed to providing our customers with transparency. As part of maintaining this trust and commitment to you, we are informing you of a recent event that affected your Microsoft-managed email account.
We have identified that a Microsoft support agent’s credentials were compromised, enabling individuals outside Microsoft to access information within your Microsoft email account. This unauthorized access could have allowed unauthorized parties to access and/or view information related to your email account (such as your e-mail address, folder names, the subject lines of e-mails, and the names of other e-mail addresses you communicate with), but not the content of any e-mails or attachments, between January 1st 2019 and March 28th 2019.
Upon awareness of this issue, Microsoft immediately disabled the compromised credentials, prohibiting their use for any further unauthorized access. Our data indicates that account-related information (but not the content of any e-mails) could have been viewed, but Microsoft has no indication why that information was viewed or how it may have been used. As a result, you may receive phishing emails or other spam mails. You should be careful when receiving any e-mails from any misleading domain name, any e-mail that requests personal information or payment, or any unsolicited request from an untrusted source (you can read more about phishing attacks at https://docs.microsoft.com/en-us/windows/security/threat-protection/intelligence/phishing).
It is important to note that your email login credentials were not directly impacted by this incident. However, out of caution, you should reset your password for your account.
If you require further assistance, or have any additional questions or concerns, please feel free to reach out to our Incident Response Team at [email protected]. If you are a citizen of European Union, you may also contact Microsoft’s Data Protection Officer at:
EU Data Protection Officer
Microsoft Ireland Operations Ltd
One Microsoft Place,
South County Business Park,
Leopardstown, Dublin 18, Ireland
[email protected]Microsoft regrets any inconvenience caused by this issue. Please be assured that Microsoft takes data protection very seriously and has engaged its internal security and privacy teams in the investigation and resolution of the issue, as well as additional hardening of systems and processes to prevent such recurrence.