Spain’s data protection authority just handed Yoti a €950,000 fine for building a biometric identity system that violated GDPR in three distinct ways.
Governments around the world are mandating age verification at an unprecedented scale, and companies like Yoti exist precisely to service that demand. The fine is a signal that the infrastructure being built to satisfy those mandates is already failing its most basic legal obligations.
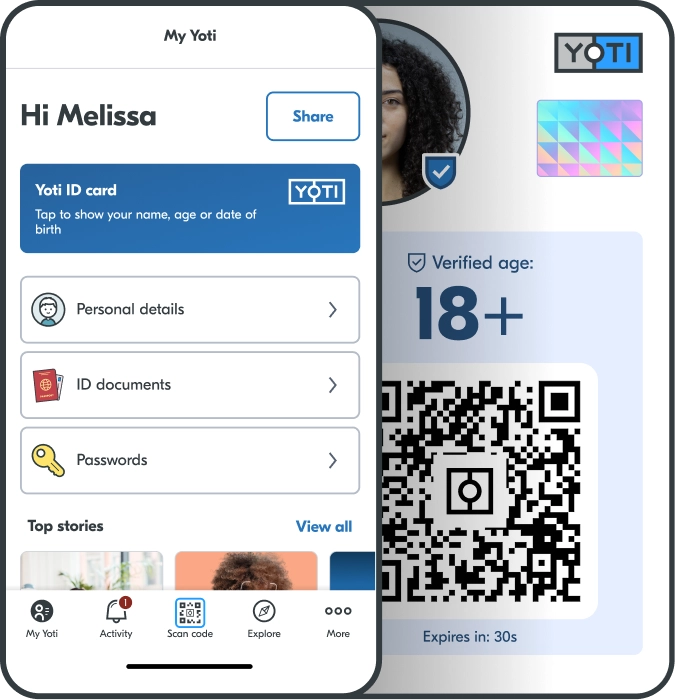
The largest penalty, €500,000, targets the core of what Yoti does. The app compares a live selfie against a stored biometric template during account setup.
Yoti called this “authentication.” Spain’s AEPD called it a unique identification of a natural person, which falls squarely under GDPR’s special category protections.
Reclaim Your Digital Freedom.
Get unfiltered coverage of surveillance, censorship, and the technology threatening your civil liberties.
Half of the United States now mandates or is considering mandating age verification for accessing adult content or social media platforms, with nine states seeing their laws take effect in 2025 alone and more coming in 2026.
The EU is moving in the same direction. The European Commission recently developed a blueprint for age verification that will be piloted in Denmark, France, Greece, Italy, and Spain.
Australia passed laws barring children under 16 from social media entirely, requiring platforms to build age verification into their services.
The legislative pressure is coordinated, accelerating, and pointed directly at companies like Yoti to deliver the technical infrastructure.
At the technical level, companies have only two tools: identity-based verification, where users upload government IDs or provide documents proving their age, or inference, where platforms guess age based on behavior, device signals, or biometric analysis, most commonly facial age estimation from selfies or videos.
The retention violations add another €250,000. Geolocation data reportedly stayed in Yoti’s systems for five years. Video recordings from liveness detection sit around for 30 days. Fraudulent identity documents submitted during failed verification are retained beyond their original purpose and repurposed to train Yoti’s algorithms.
A document submitted as evidence of fraud becomes a permanent training asset. The person who submitted it never agreed to that.
Discord disclosed last year that hackers breached a vendor doing age verification services. In that single breach, around 70,000 people had their government ID cards exposed, now presumably available to cybercriminals.
That’s one incident from one vendor. These companies should also be anticipated as targets for state-backed hackers, given that a database linking real identities to online behavior is exactly the kind of intelligence asset that foreign governments pursue.
Yoti pushed back hard, with an appeal. “Yoti rejects in the strongest possible terms the decision of the AEPD and has begun the appeal process to the Spanish High Court,” the company said in a statement, adding that “no personal data of any app user has been breached or compromised in any way.”
The company also disclosed something notable about the investigation’s conduct: “We fully cooperated with the AEPD’s information requests, but we were never notified that we were under investigation.”
The appeal doesn’t change the six-month compliance deadline.
Yoti has six months to demonstrate to the AEPD that its biometric data processing, consent mechanisms, and data retention practices comply with GDPR.
That’s the bar. Not whether mass biometric identity verification is proportionate to the goal of keeping teenagers off adult content. Just whether this particular company stored the face scans for slightly too long and made the opt-out slightly too hard to find.
The larger question, whether governments should be mandating this infrastructure at all, isn’t part of the proceeding.